Many teams are confident they have virtual machine access under control. Interactive access is tightly restricted.SSH and RDP are only…
 aws azure cloud infrastructure pentests Cloud security entraid
aws azure cloud infrastructure pentests Cloud security entraid
Why Cloud Infrastructure Pentests Matter
Cloud compliance assessments don’t tell you how you’ll actually be breached.
Cloud infrastructure pentests exist for that exact reason.
Here’s where the difference really matters…
 azure Cloud security
azure Cloud security
Discovering Attack Paths in Microsoft Azure for Enhanced Security
We’re changing the way consultants assess Azure Subscriptions and detect Attack Paths. All you need is “Reader” access to an…
 azure Cloud security
azure Cloud security
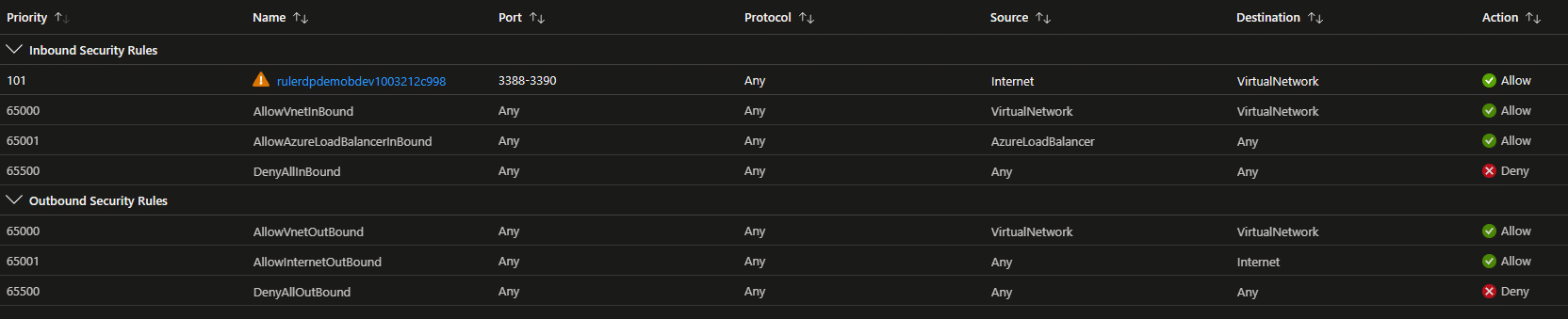
Top 5 Azure VM Security Blunders That Get You Owned
Top 5 Azure VM Security Blunders that will get you owned As more and more businesses embrace Azure Virtual Machines…
 azure Cloud security
azure Cloud security
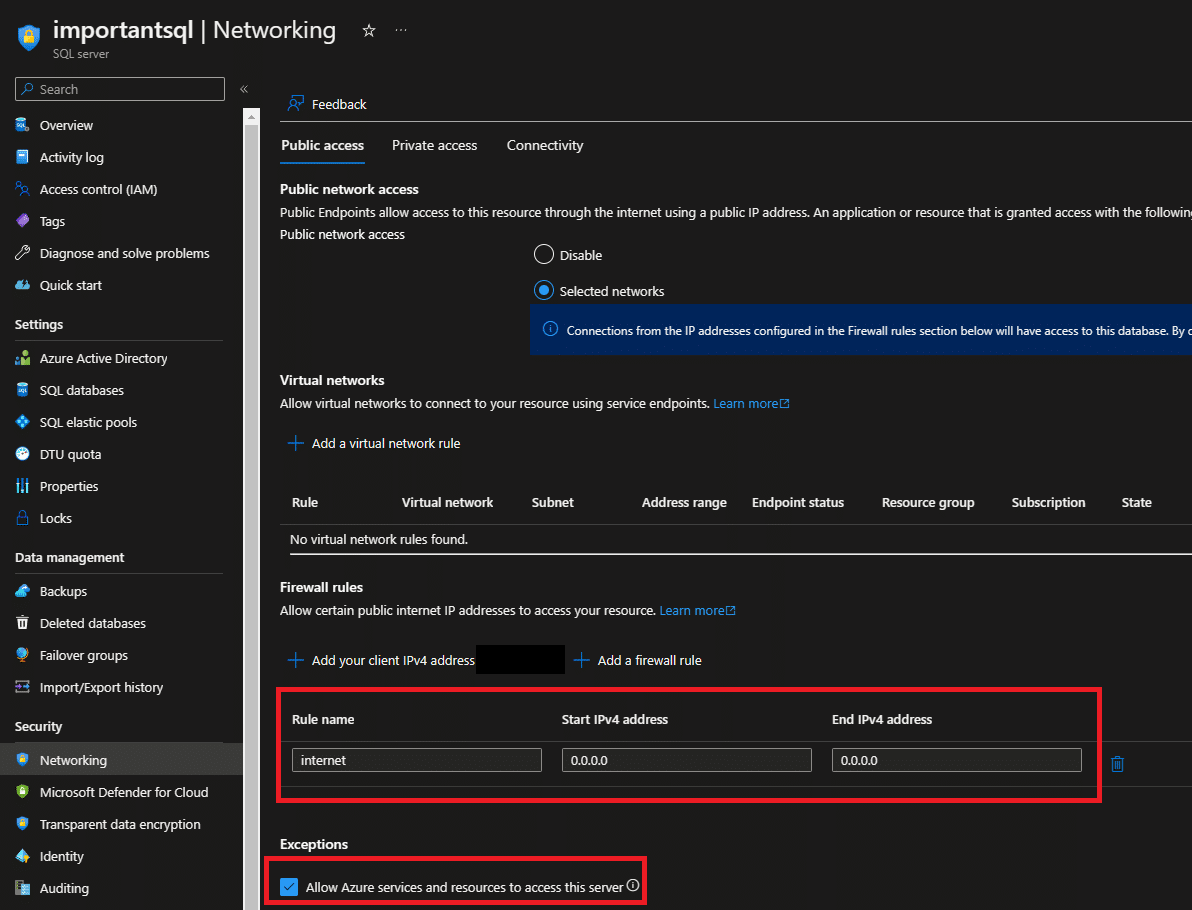
Is Your Azure SQL at Risk? Learn How to Secure It with this Step-by-Step Guide
Azure SQL is a cloud-based relational database management system that is widely used by businesses and organizations around the world.…
 azure Cloud security
azure Cloud security
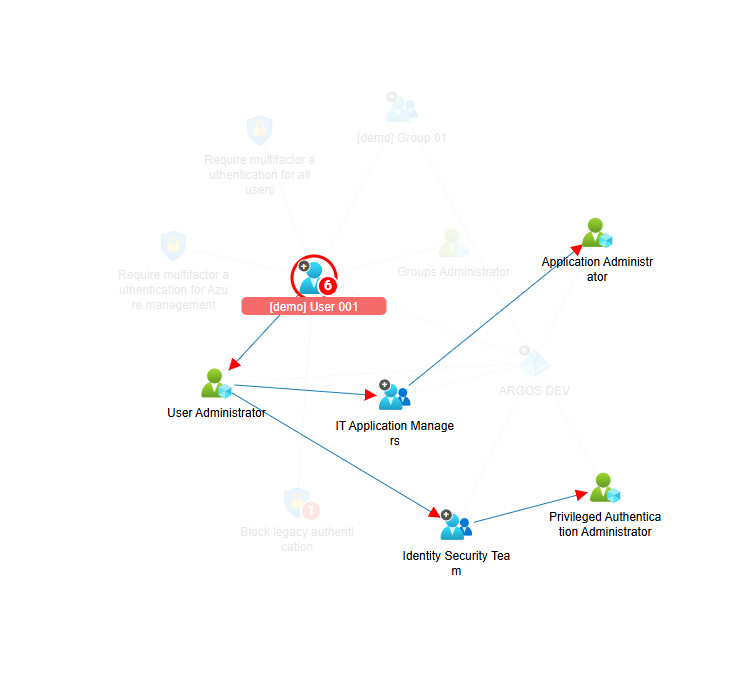
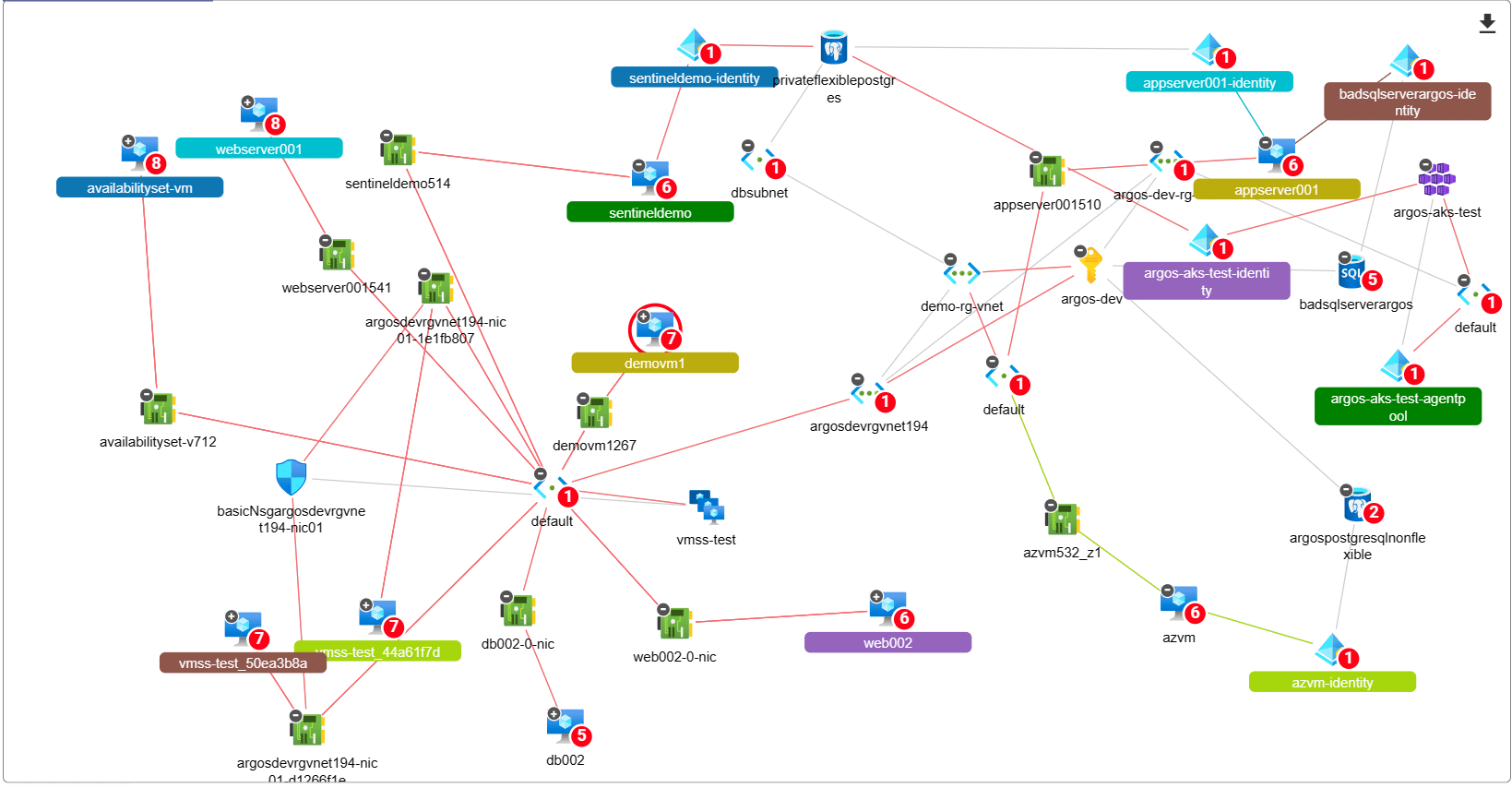
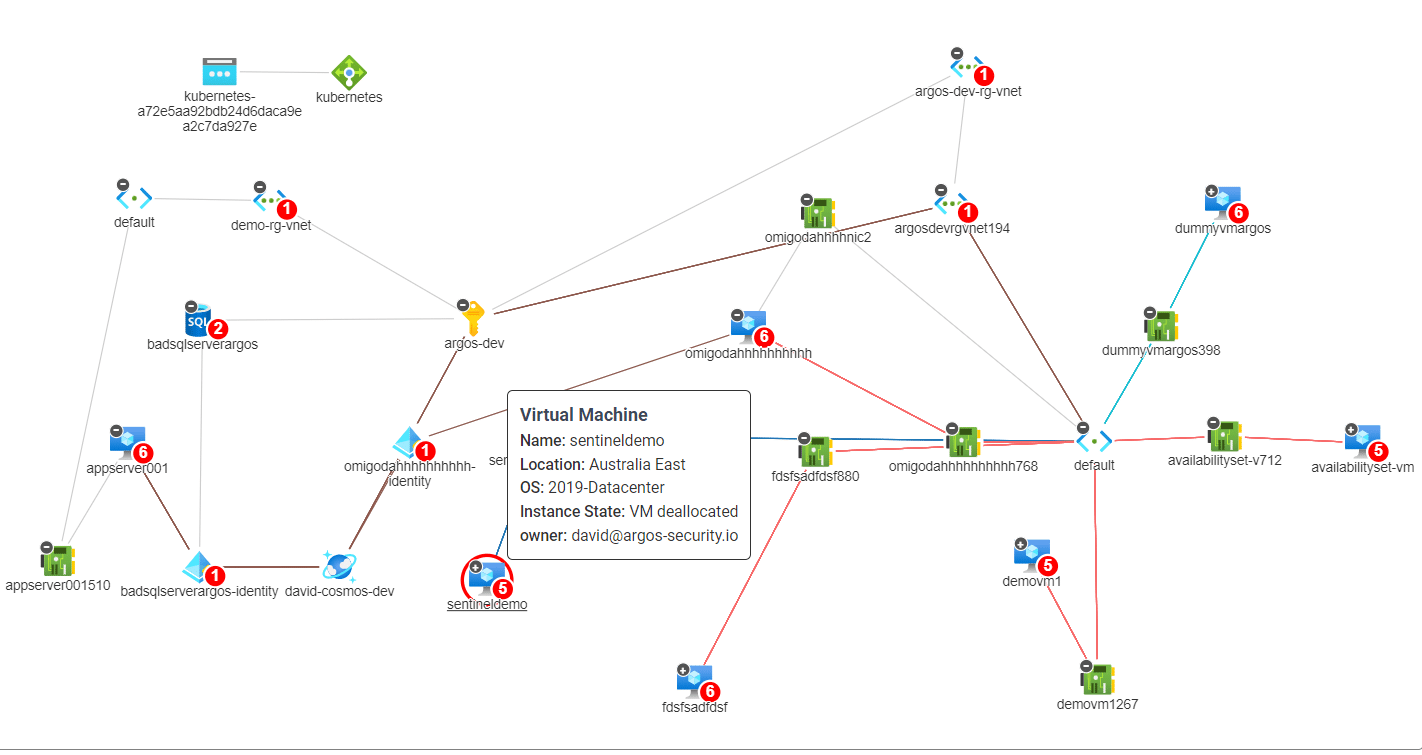
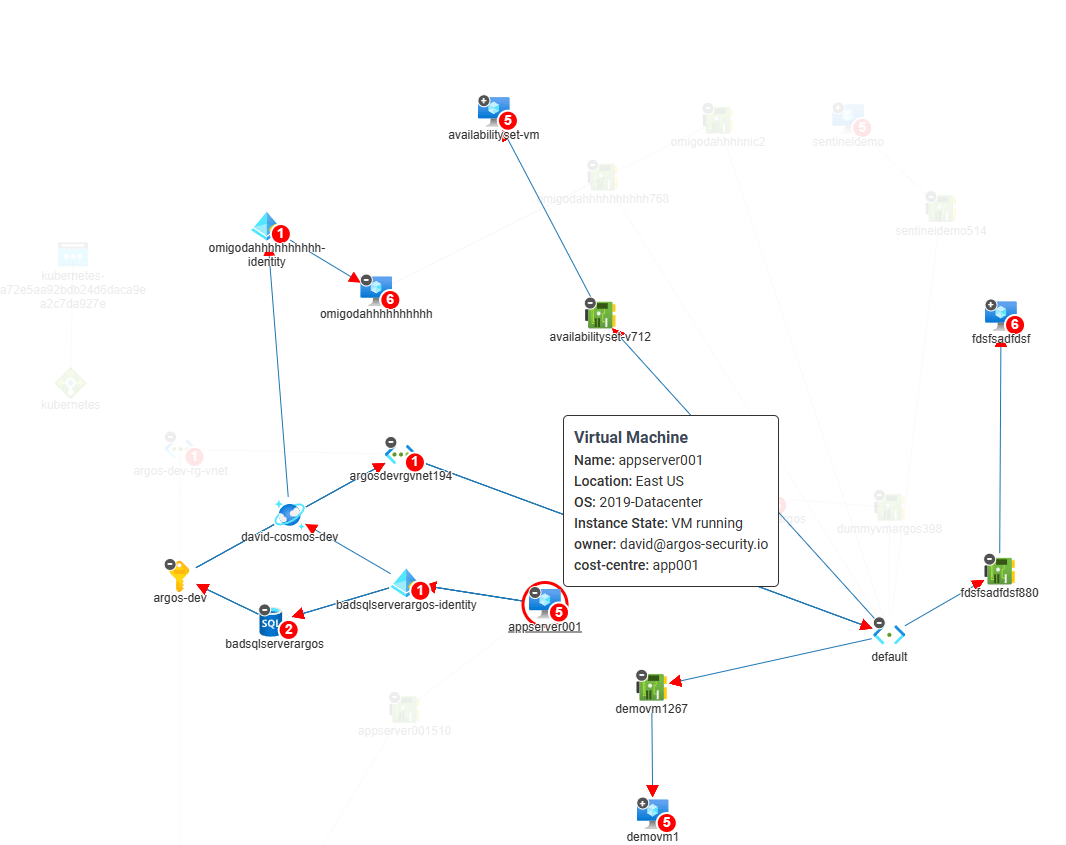
Identifying and Securing Hidden Attack Paths in Azure Infrastructure
Lateral movement attacks are a significant risk facing organizations that operate in the cloud. These attacks occur when an attacker…
 Cloud security Start up
Cloud security Start up
Why We Started ARGOS – Cloud Security FOR Consultants
Today, we wanted to give you a little history lesson into why we started ARGOS. What lead us to build…
How to make sense of CSPM, CAASM, CIEM, CNAPP
Did you come here because you typed “What is CSPM” or “Do I need a CIEM?” into the search engine?…
 Cloud security CSPM
Cloud security CSPM
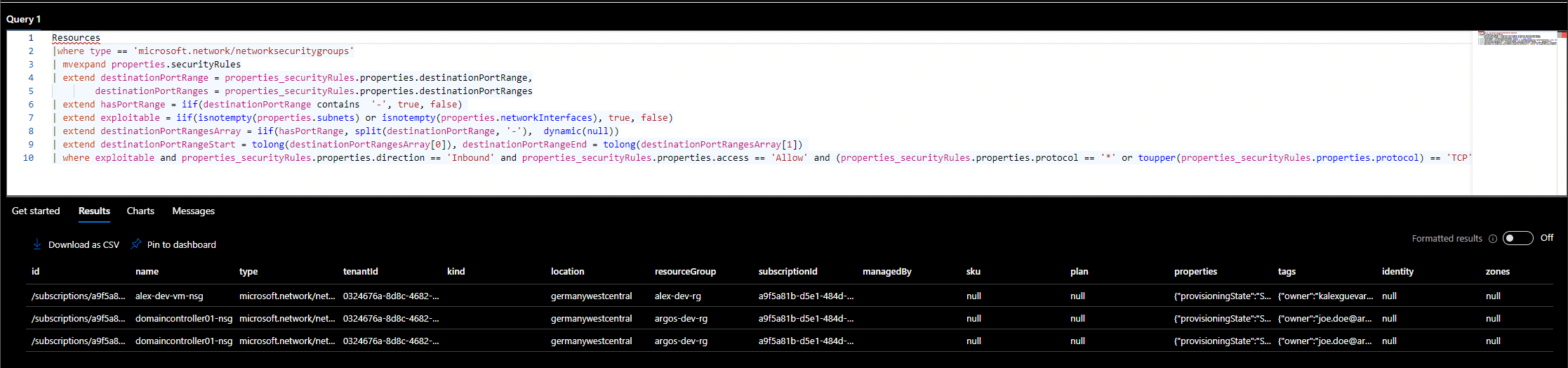
How To Monitor For Risky Public Azure Virtual Machines
Public Azure Virtual Machines are one of the most exploited resources in the Azure cloud. As we mentioned in our…
Azure CosmosDB Vulnerability – What do I need to do?
Just recently Wiz released an announcement into a very critical vulnerability in one of Microsoft Azure’s flagship services, Azure Cosmos DB. Because these…
